Uncovering Vulnerabilities: Security Flaws Discovered on the Indian Prime Minister’s Website
Hello geeks, Biswajeet Ray Here, Security Engineer, OSINT & Threat Analyst.
I’ve been acknowledged by Microsoft, IBM, Lenskart, Shaadi.com, Panasonic, HP and many companies and governments for reporting security vulnerabilities in their web applications.
Disclaimer: I am writing about how i found and reported vulnerabilities in Our Prime Minister Narendra Modi site. We Indians always ready to contribute for our nation.
Let's start,
Before Independence Day I sudden remember that our PM is protected by SPG. But what about his websites. So as an Indian I remembered my fundamental duties always nation first.

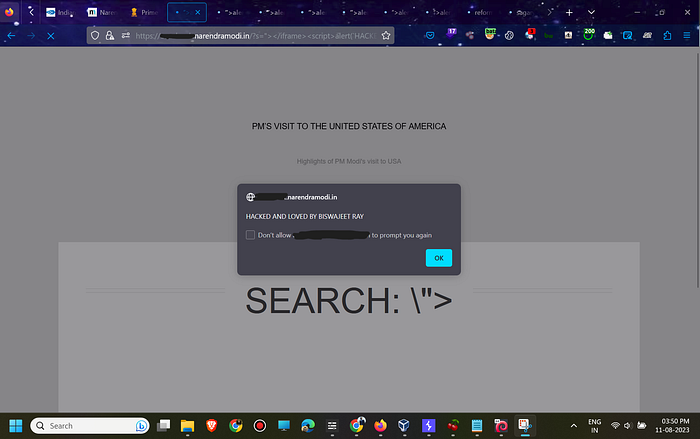
Then i started hunting on our PM site so the first vulnerability found by me is Cross site scripting (XSS)
(1) I found approx 8 subdomains vulnerable to Cross Site Scripting
param “s=” used payload %22%3E%3C/iframe%3E%3Cscript%3Ealert(`HACKED%20AND%20LOVED%20BY%20BISWAJEET%20RAY`);%3C/script%3E%3Ciframe%20frameborder=%220%EF%BB%BF
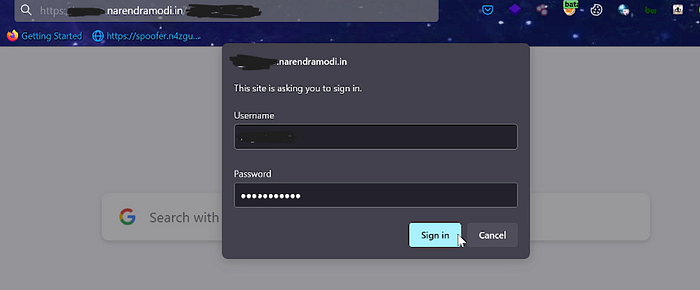
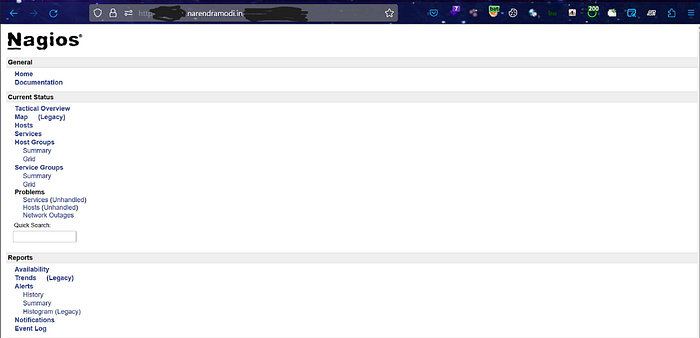
(2) Unauthenticated Access via Default Credentials
After finding XSS i found Unauthenticated access which gives me unauthenticated access to Nagios dashboard
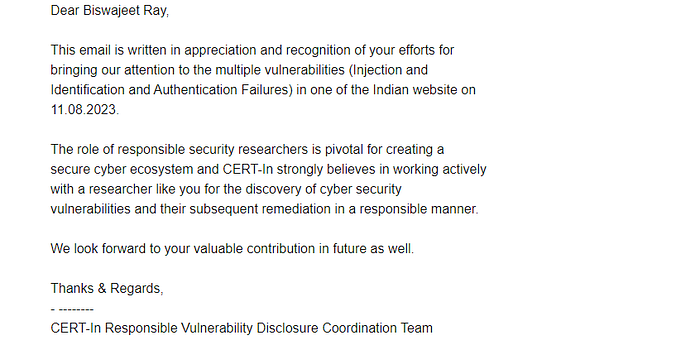
I immediately reported it to incident@cert-in.org.in with POC
Response by CERT-IN and PMO Team
Aug 11, 2023 : Reported
Aug 14, 2023 : A ticket was assigned.
Aug 21, 2023 : The issue was resolved (Retested)
Aug 21, 2023: Acknowledged by CERT after verification and fixes from PMO.
Kudos to CERT-IN team for fast response and fixes.
Thanks for reading. Keep securing internet. Always remember nation first.
For more you can contact me here:
https://www.linkedin.com/in/biswajeet-ray-397742200/ [Linkedin]
https://twitter.com/BiswajeetRay7 [Twitter]
